Understanding Port Usage
XDR Forensics uses specific ports to manage communication between the XDR Forensics Console, responders, and other components of the system. Ensuring that the correct ports are open and configured can prevent connectivity issues and optimize performance. Below is a breakdown of the key ports used by XDR Forensics and their purposes.
Key Ports Used in XDR Forensics
Section titled “Key Ports Used in XDR Forensics”-
TCP 443: This is the default port for most XDR Forensics communications, including:
- XDR Forensics User -> Console: Used for users accessing the XDR Forensics Console.
- Asset -> Console: Used by responders on assets to communicate with the console. This is the default and preferred port, in some cases, users may wish to switch to 8443:
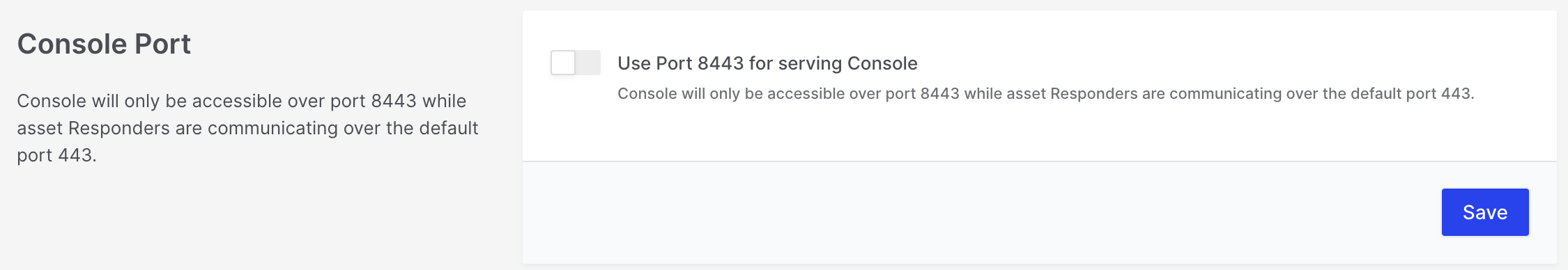
Understanding Port Usage: Console Port
- Responder Downloads: The responder download links (on the deploy page) are accessible via port 443. Using this port ensures consistent download access, especially in environments where only port 443 is available.
-
TCP 8443: This is an alternative port used for user access to the console, as well as other specific functions, including:
- XDR Forensics User -> Console: Optional port for user access to the XDR Forensics Console.
- Shareable Deploy Page: The shareable page for responder deployment is available on this port.
- Off-Network Tasks: The download links for tasks that run off-network are accessible on this port.
- Admin Portal: The administrative portal operates on this port.
- REST API: API calls to the XDR Forensics Console (
api/public/*) are handled on this port. - Azure and Okta SSO: If you’re using Azure or Okta Single Sign-On (SSO), the callback from within the browser should happen over port 8443.
-
TCP 4222: This port is used for real-time task pushes to assets. If real-time communication is needed for task assignment, this port should be enabled.
-
TCP/UDP 389 and 636: These ports are optional and used when Active Directory (AD) integration is enabled:
-
389: For LDAP (Lightweight Directory Access Protocol) communication.
-
636: For LDAPS (LDAP over SSL) communication.
-
TCP/UDP 514: This is the optional port used when Syslog integration is enabled. Syslog helps in forwarding system logs to a centralized log server.
Recommended Usage
Section titled “Recommended Usage”While port 8443 can be used manually for downloading responders and accessing the console, we strongly recommend using port 443 for the following reasons:
- Consistency: Port 443 is universally available across most environments and networks, reducing the risk of connectivity issues.
- Responder Communication: Responders may not have access to port 8443 in certain configurations, making port 443 the preferred choice for ensuring reliable responder-console communication.
Summary of Port Functions:
| Port | Function |
|---|---|
| TCP 443 | Default for user and responder communication with XDR Forensics Console |
| TCP 8443 | Optional for user access, API, and other console functionalities |
| TCP 4222 | Enables real-time task pushes to assets |
| TCP/UDP 389/636 | LDAP and LDAPS for Active Directory integration |
| TCP/UDP 514 | Syslog port for logging |
By ensuring that these ports are correctly configured and open, you can optimize communication between the XDR Forensics Console and responders, allowing for seamless operation.